Crypto Transaction Monitoring Gaps Regulators Now Flag
In 2023, Binance settled for a payment of 4 billion dollars to resolve what the U.S. Department of Justice called the largest corporate criminal settlement in DOJ history at the time.
It was inadequate cryptocurrency transaction monitoring, a compliance failure that regulators had flagged, warned against, and ultimately penalized at a scale the industry had never seen.
The Binance case was not an isolated failure. It was the largest enforcement action in compliance history against a firm whose monitoring controls were auditable, documented, and consistently inadequate. The question is not whether your program could survive the same scrutiny, it is whether you know the specific points where it would fail.
Why Legacy AML Logic Fails in Crypto?
Banks and financial institutions expanding into virtual asset services frequently make a recurring structural error: they extend their existing transaction-monitoring frameworks for cryptocurrencies directly to digital asset activity. The logic is understandable.
Legacy AML systems assume embedded counterparty identity and centralized payment rails. Blockchain transactions carry no native identity, and fiat-calibrated thresholds cannot interpret wallet behavior or address-level risk patterns.
Three structural failure points explain why legacy AML logic cannot be directly applied to blockchain activity.
- Crypto operates at a speed that renders batch-processing cycles operationally useless, layering can complete multiple wallet hops before a traditional monitoring window closes.
- Rule-based thresholds calibrated for fiat behavior cannot interpret patterns in blockchain addresses.
- Counterparty identity is not structurally embedded in a crypto transaction, a wallet address reveals nothing about its controller.
These are not configuration problems, they are architectural gaps that require purpose-built monitoring frameworks.
For crypto VASPs, the vulnerability is different but equally serious. Many have built monitoring functions reactively, adding tools as regulatory pressure mounted, without architecting a coherent program underneath. The result is coverage that looks complete on paper but breaks down when regulators look closely.
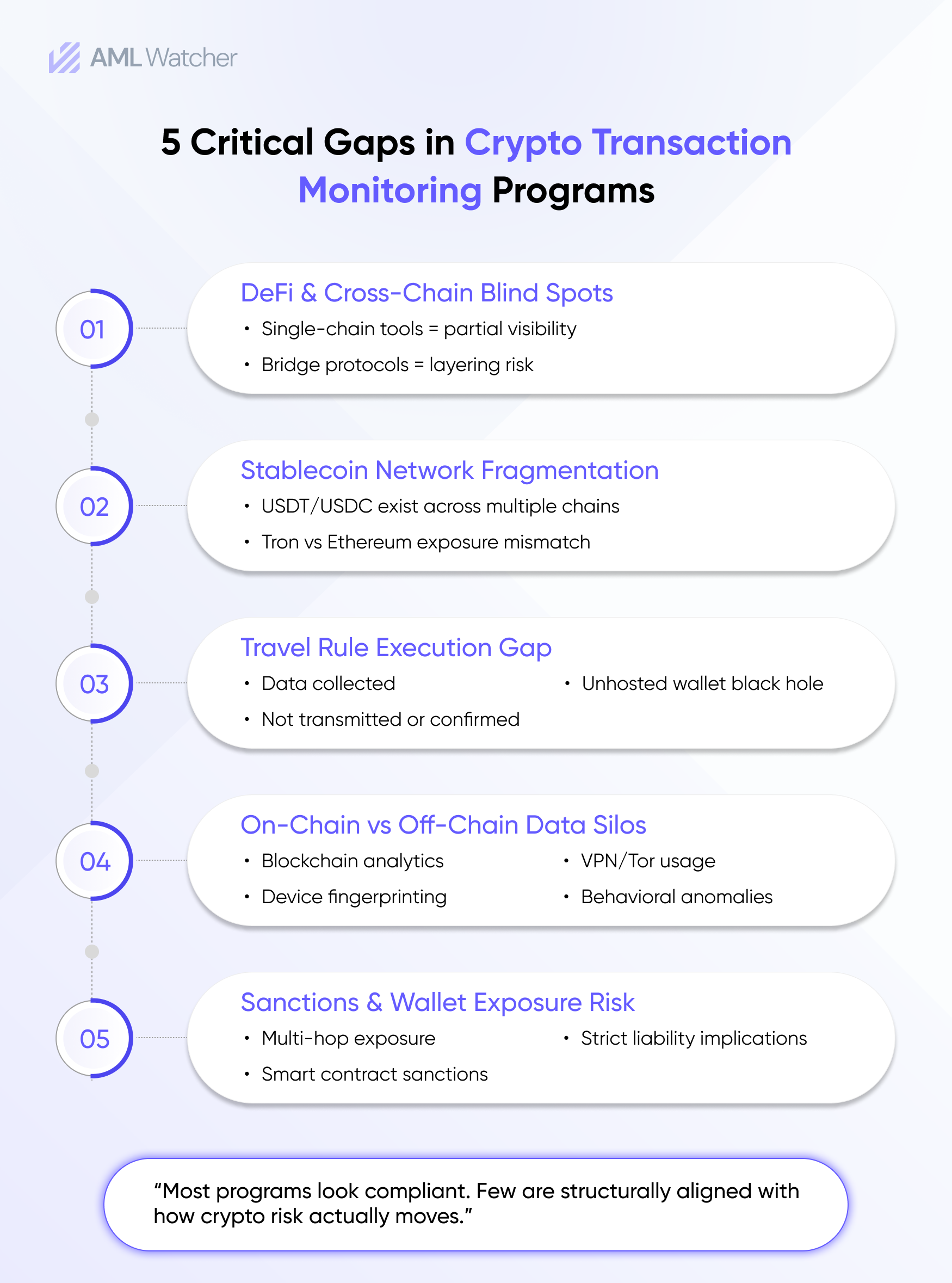
What Current Crypto Transaction Monitoring Programs Are Missing
DeFi and Cross-Chain Activity
The Financial Action Task Force clarified in its updated virtual asset guidance that entities exercising sufficient control or influence over DeFi arrangements may fall within the definition of a VASP. This interpretation has direct implications for platforms facilitating access to decentralized protocols. Most crypto transaction monitoring programs have not operationalized a response to this yet.
Cross-chain bridging compounds the issue in a meaningful way. Moving assets from Ethereum through Solana to BNB Chain via bridge protocols is now a documented method for obscuring fund origin, chosen because many monitoring tools remain limited to single-chain visibility, fragmenting transaction continuity, and weakening origin tracing.
Stablecoin Flows
Stablecoins represent a growing proportion of illicit transaction volume for USDT and USDC, which offer dollar-denominated value, near-instant settlement, and liquidity depth across dozens of platforms simultaneously. The same stablecoin exists on more than one blockchain at a time. A program screening USDT on Ethereum but not on Tron, which has historically carried disproportionate high-risk stablecoin volume, is working from an incomplete dataset.
Stablecoin screening must cover every chain where an asset is issued, especially USDT on Tron, which has a significant amount of high-risk volume highlighted by FATF and FinCEN. Screening only on Ethereum creates a blind spot.
The Originator/Beneficiary Transmission Requirement Execution Gap
Many VASPs collect originator and beneficiary data but fail at secure transmission, confirmation of receipt, and unhosted wallet handling. Collection without verified transmission does not meet Travel Rule expectations. What remains broken at the majority of organizations is transmission, securely sharing that data with a counterparty VASP, confirming receipt, and managing the unhosted wallet case where there is no licensed counterparty to receive it. Collecting data that fails to reach its destination is not Travel Rule compliance. Regulators are beginning to treat the distinction seriously.
How is On-Chain and Off-Chain Integration Different?
Blockchain transaction monitoring surfaces what happened on-chain. It does not explain who drove the activity or why the behavioral pattern looks the way it does.
A customer with a clean wallet history can remain a substantial risk. The data points that uncover it, VPN or Tor usage obscuring where the user is connecting from, what device they’re using, fingerprint changes between sessions, login timing anomalies, and inconsistency between stated transaction purpose and actual fiat deposit behavior, exist entirely off-chain. They live in platform information that the majority of programs treat as operationally separate from their AML function.
A customer who clears on-chain screening but triggers multiple off-chain anomalies represents a risk that fragmented systems miss. Exchanges and institutions with mature AML compliance programs combine both data streams into a unified risk system.
What AI Delivers in Crypto Monitoring, and What It Cannot
A realistic assessment of AI in crypto monitoring is more useful than the hype. Adaptive risk model-driven cryptocurrency transaction monitoring tools actually enhance three things:
- Active entity behavior profiling that adapts to customer activity.
- Multi-hop tracing of fund flows through complex transaction graphs.
- Reduction of false positives at the volumes of transactions that crypto platforms are working with.
When machine learning models are appropriately tuned, they can minimize the false positive volumes by focusing on high-risk behavioral signals as opposed to transaction-specific thresholds. That cannot be considered an efficiency metric; it is an investigative quality result. Analysts freed from alert noise can focus on cases that warrant genuine investigation.
The limitation most often underestimated is explainability. Supervisory authorities require documented, auditable reasoning for model-generated alerts. If a system cannot produce traceable justifications, it creates governance risk instead of mitigating it.
AML Watcher’s TruRisk Agent is built around this requirement. It generates a written justification for every alert it produces, documenting the specific signals, transaction patterns, and risk indicators that triggered the flag. Analysts and examiners have a documented record of the model’s reasoning, not a black-box score.
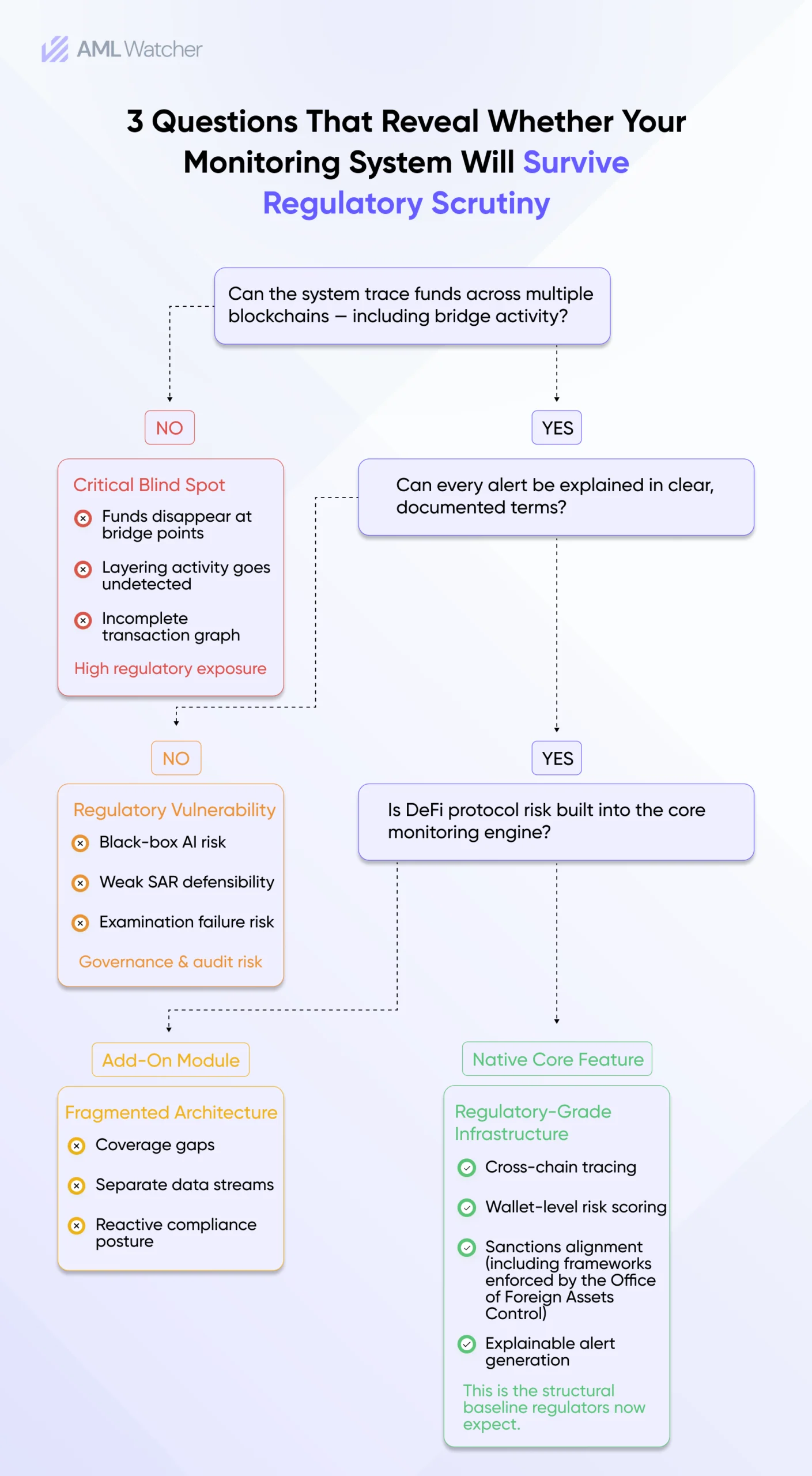
How Is a Regulator-Ready Crypto Monitoring Program Built
Regulatory examiners are not reviewing the compliance policies. They are testing whether the controls produce the outcomes described by those policies. Three components consistently separate programs that hold up from those that don’t.
Wallet-Level Risk Scoring Beyond KYC
A verified customer with clean documentation can hold a wallet with direct exposure to a sanctioned address or a known mixing service. KYC establishes identity at onboarding. On-chain behavior is a separate question entirely. Counterparty wallet screening is now a baseline expectation in regulatory examinations of traditional institutions and crypto platforms, not a differentiating capability.
Sanctions Screening as a Distinct Program Layer
OFAC’s strict liability standard carries no intent requirement. Processing a transaction that touches a designated wallet address constitutes a violation, no matter what the institution’s knowledge or the number of intermediary hops involved. The 2022 Tornado Cash designation extended this further by establishing that a smart contract itself can be sanctioned. Though the legal status of that designation has faced ongoing court challenges, compliance teams should monitor it.
In 2021, BitPay settled with OFAC for $507,375 for processing transactions involving users in sanctioned regions. The violations OFAC attributed to inadequate sanctions screening controls rather than intentional conduct. The operational consequences this carries for cryptocurrency transaction monitoring software integrations are still being resolved across the industry.
SAR Quality as a Program Health Indicator
Regulators across jurisdictions have communicated, with increasing directness, that high-volume, low-quality SAR filings reflect miscalibration, not diligence. A filing that includes wallet attribution data, transaction flow visualization, and a structured explanation of suspicious indicators provides materially greater investigative value than reports based solely on transaction frequency anomalies. Financial institutions entering crypto and established VASPs are each being held to higher standards for SAR quality as an indicator of the program’s overall maturity.
Choosing Cryptocurrency Transaction Monitoring Software
Most vendors pass feature checklists. Few pass regulatory scrutiny.
Cross-chain tracing capability is the operational dividing line between cryptocurrency transaction monitoring software built for the current risk environment and tools that have not kept pace with how illicit actors actually move funds.
If a vendor qualifies that capability with add-on pricing or cannot answer clearly, that response is itself a data point. Key questions to ask include:
- How does your model generate and document alert justifications for regulatory review?
- How is Travel Rule transmission handled for unhosted wallets?
- Does your platform trace funds across chains natively, or only within a single blockchain?
- What is your update cadence when new sanctions designations are issued?
What Regulators Are Examining During Crypto AML Reviews
Supervisory examinations of virtual asset programs are focusing on four recurring themes:
- Evidence of risk assessment specific to blockchain typologies
- Cross-chain tracing capability
- Travel Rule transmission controls, not only data collection
- Model governance and explainability documentation
Monitoring Is a Strategic Position, Not a Compliance Checkbox
Treating crypto monitoring as a formality exposes institutions to escalating supervisory risk. For cross-chain tracing across Ethereum, Tron, BNB Chain, Solana, and 20+ additional networks, AML Watcher’s Crypto Wallet Screening reconstructs layering patterns that single-chain tools cannot follow.
AML Watcher is a blockchain risk intelligence platform that offers wallet exposure screening and cross-network tracing designed to support regulatory defensibility. Its surveillance systems generate written alert justifications that meet the supervisory review requirements.
Organizations subject to virtual asset regulations need documented evidence of monitoring coverage across all relevant blockchains, not just those for which their legacy tools were built.
Frequently Asked Questions
Move Beyond Articles. Activate AML Intelligence.
Switch to AML Watcher today and reduce your current AML cost by 50% - no questions asked.
- Find right product and pricing for your business
- Get your current solution provider audit & minimise your changeover risk
- Gain expert insights with quick response time to your queries