Money Mule Detection: APP Fraud and AML Convergence in 2026
The Financial Conduct Authority reported an increase of over 207,000 personal accounts as money mule accounts in 2024, indicating a 22% year-on-year rise in the number of institutions monitored.
Regulatory and law enforcement data indicate that money laundering and fraud are both on the same upward trajectory. The number of fraud offenses in the UK alone reached 4.16 million in the year ending 2025, 31% higher than previous years, with money laundering cases also increasing 36% annually, showing that the burden of enforcing illicit fund flows is on the increase.
For analysts working on Anti-Money Laundering (AML) and fraud at retail banks and payment processing platforms, this number reveals a significant problem. The accounts that allowed the money laundering had already completed the onboarding process. They remained part of the customer base and were making transactions that standard AML monitoring could not detect.
What is a Money Mule in the Context of Anti-Money Laundering
Money mule accounts are the financial accounts that are used to receive and transfer illegal money on behalf of criminals. These accounts can be owned by either those who knowingly engage in laundering or by those who are manipulated to join in scams or participate in fake employment opportunities. In both cases, the account becomes a transit point in the laundering chain that makes detection critical for institutions under AML obligations.
Why APP Fraud and AML Are Now the Same Problem
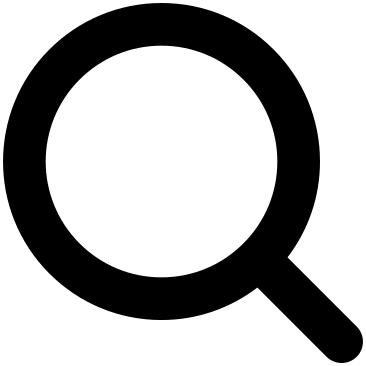
Authorized Push Payment (APP) fraud and money laundering are not separate crimes that happen to share a payment rail. They are consecutive phases of one criminal operation. In a scam, a victim authorizes a payment, investment fraud, romance scam, or impersonation of a government agency or a bank, and those funds immediately begin moving through a chain of mule accounts before being aggregated, withdrawn, converted to stablecoins, or sent cross-border.
The fraud team sees the originating transaction and chases recovery. The AML team monitors downstream account activity and attempts to file a Suspicious Activity Report (SAR). Neither team, working alone, sees the full chain. That’s the gap organized crime keeps walking through that fraud teams do not see what AML teams see, and vice versa, and organized crime has been exploiting it.
These flows become more complex as they move across multiple accounts in brief time windows designed to break traceability across fraud and AML systems.
INSIGHT
Fraud and AML teams monitor different parts of the same chain, creating a visibility gap that organized crime exploits.
From Scam to Laundering: Transaction Lifecycle
A typical fraud transaction follows a conventional and expected lifecycle. Funds originate from a victim authorization, move into one or more mule accounts, and are quickly laundered through multiple transfers to an unclear origin. In advanced cases, proceeds are consolidated and moved to offshore accounts or converted into digital assets. Every stage strengthens layering patterns that diminish the visibility when accounts are analyzed in isolation.
Authorized Push Payment Fraud Typologies Feeding the Networks
According to regulatory information, online channels initiate 70% of APP fraud cases. This outlines how digital platforms facilitate money laundering through mule networks. The fraud-AML intersection in 2026 is driven by specific authorized push payment typologies that generate distinct mule activity patterns, each requiring different detection logic.
Romance scams and investment fraud produce high-value, single-leg transfers that land in accounts specifically opened or conditioned to receive them. The mule, sometimes unwitting, sometimes fully complicit, has either been groomed into receiving funds on behalf of a fictitious “partner” or recruited through fake employment ads promising commissions for processing transfers.
Impersonation scams targeting retail banking customers produce rapid fund movements where the victim believes they are protecting their own money. The receiving account usually has a limited history of transactions, which results in a sparse behavioral baseline and lower confidence in alerts.
Business email compromise (BEC) generates corporate wire transfers that often exceed retail fraud thresholds, move through accounts that maintained normal transaction patterns for months before activation, and frequently involve mule accounts at correspondent banks rather than the same institution as the victim.
How Mule Networks Are Recruited
Money mule networks are not formed randomly. Recruitment often occurs via social media platforms, fake employment listings, and romance-based manipulation schemes. Victims are persuaded to “help transfer funds” or offered commission-based functions that include processing payments. Younger and financially susceptible individuals are frequently targeted, increasing exposure to mule recruitment at scale.
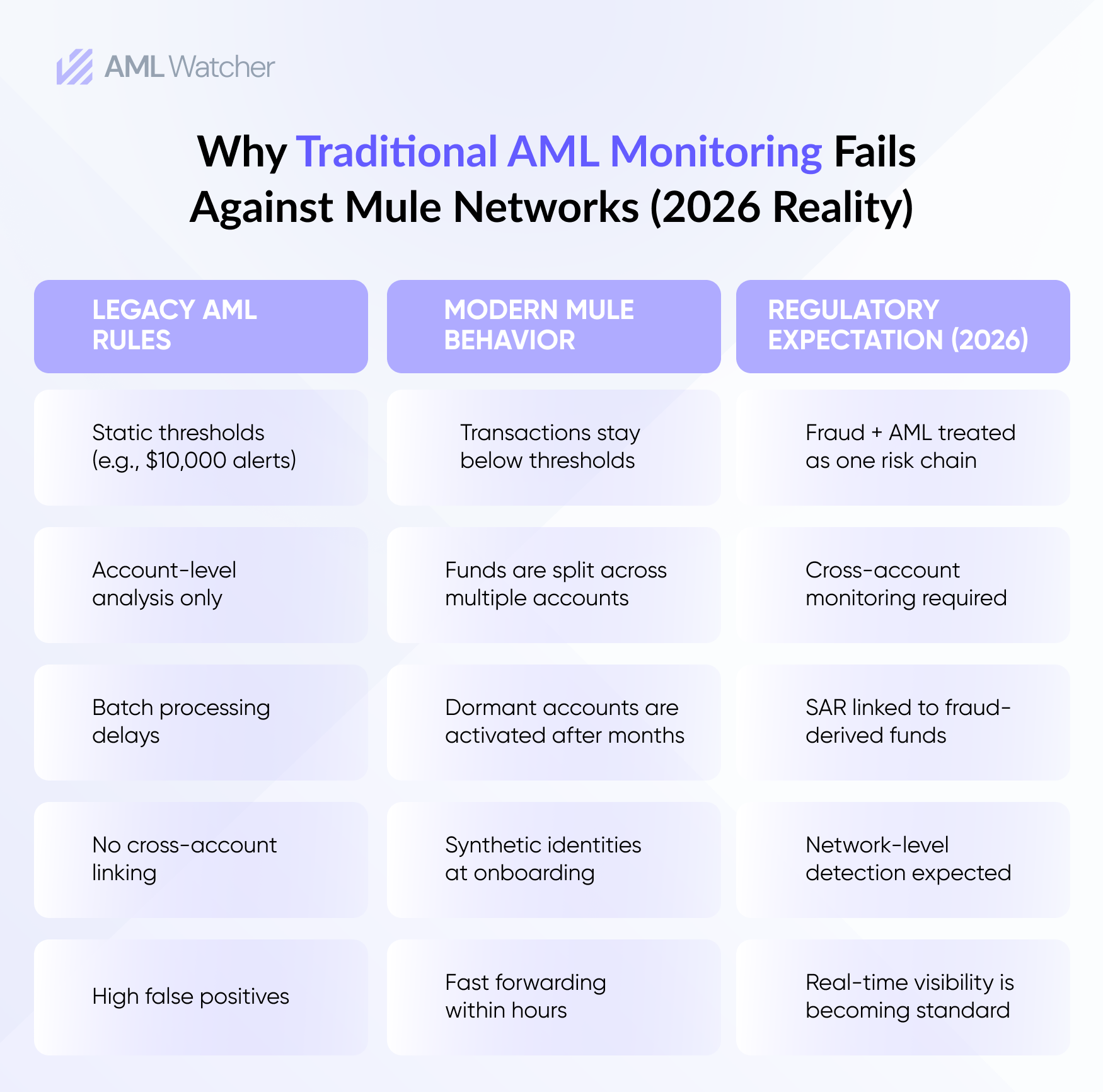
A single threshold-based rule, flag large inflows within days of account opening, will miss BEC-linked mule accounts that were dormant for six months first. It will also fire excessive alerts on simpler typologies, adding to alarm fatigue that is already a structural problem in AML operations.
These recruitment patterns later appear in transaction monitoring as distinct signals of the behavior, such as sudden inflows, structuring, and rapid forwarding. Witting mules often run recurring small transfers and deliberate structuring just below reporting thresholds. Complicit mules frequently originate with synthetic identity data at onboarding, which makes the problem indivisible from a KYC failure from day one.
The OCC’s Signal and the 2026 Regulatory Direction
The OCC Semiannual Risk Perspective of Spring 2025 classified compliance risk as high, specifically mentioning BSA/AML and consumer compliance risk associated with high levels of fraud and access issues. The report solidified that the examiner’s scope encompasses the assessment of fraud identification and quality of investigations, along with the filing of SARs all collectively instead of individually.
That framing reflects what practitioners have observed in operations, and regulators are now formalizing. A fraud event that results in funds passing through a mule account at your institution is a BSA/AML failure. The institution processing the mule-side of an APP fraud transaction carries monitoring obligations regardless of whether it also serviced the victim.
Examiners will look closely at how well institutions understand fraud and the money that comes from it. Regulators want to see if institutions can track fraud-related money flowing through their customers and whether their systems can catch it. If the fraud department handles a fraud loss but the Anti-Money Laundering team does not file a Suspicious Activity Report (SAR), examiners will identify the gap.
This matches the growing global expectations from FATF and FinCEN. They increasingly see fraud-related mule activity as a failure in AML controls, rather than just a separate fraud issue.
Why Legacy Monitoring Keeps Missing This
Rule-based transaction monitoring system was built for a different threat environment. The main idea is to set a limit and send an alert when a transaction goes over it. Nevertheless, this approach cannot identify mule networks that intentionally keep each transaction below the limit at all times. The network is not visible to rules that evaluate each account individually.
Batch processing compounds the problem. In real-time payment environments, overnight batch cycles generate alerts after funds have already cleared the mule account and moved on. Detection arrives too late to matter.
The deeper issue is siloed data. When fraud and AML teams run separate platforms with distinct data models and alert workflows, the intelligence that would expose a mule account is split between two systems that do not communicate. A fraud team’s confirmed mule identification never reaches the AML team’s monitoring model at the receiving bank. The pattern that would close the case for the two teams is invisible to each of them.
Industry-wide data collaboration, federated approaches where confirmed mule account intelligence is shared anonymously across institutions, is beginning to address the cross-bank visibility problem. But the prerequisite is that institutions first resolve their own internal silos.
INSIGHT
Mule networks are not detected solely by stricter rules; they are detected by shifting from account-level monitoring to network-level intelligence.
What Effective Mule Detection Looks Like
Successful mule detection programs are assessed not just by the number of alerts generated, but also by the quality of investigations that follow. The critical indicators consist of fewer false positives, quicker transitions from alert to case resolution, and higher conversion rates for suspicious activity reports related to fraud-linked accounts. Institutions with mature models also track cross-account linkage precision to assess network-level detection, and not just isolated transaction detection.
Closing the fraud-AML gap requires monitoring systems that require individual transaction analysis and focus on behavioral networks across accounts. Real-time detection, entity resolution, and adaptive typologies are now essential components of identifying mule activity at scale before funds exit the financial system.
How AML Watcher Supports the Fraud-AML Convergence Agenda
The financial system is still experiencing the effects of money laundering caused by fraud. Over £1.17 billion in losses to fraud were reported in the UK alone in 2024, and institutions detected over 1.45 billion in unauthorized fraud, indicating the size of the threat and inadequacy of the existing controls.
Money mule exposure is also rising because APP fraud networks are developing outpacing the standard monitoring systems, posing regulatory and operational risk to financial institutions that still employ siloed fraud and AML practices.
Move Beyond Articles. Activate AML Intelligence.
Switch to AML Watcher today and reduce your current AML cost by 50% - no questions asked.
- Find right product and pricing for your business
- Get your current solution provider audit & minimise your changeover risk
- Gain expert insights with quick response time to your queries